Remote Desktop Manager
Features and Highlights
Secure Access to Critical Assets
Based on the principles of a role-based access control and least privileges, it is critical to securely and centrally control and manage access to privileged accounts and critical assets by provisioning password access to users.
Account Brokering
Directly inject credentials into end servers, systems, applications and websites with just one click using our Devolutions Web Login browser extension.
Because end users never see the plain text credentials since they are automatically brokered to them, they can never compromise any information, and this greatly increases security.
Improve productivity by allowing administrators to access systems without having to find or track down credentials.
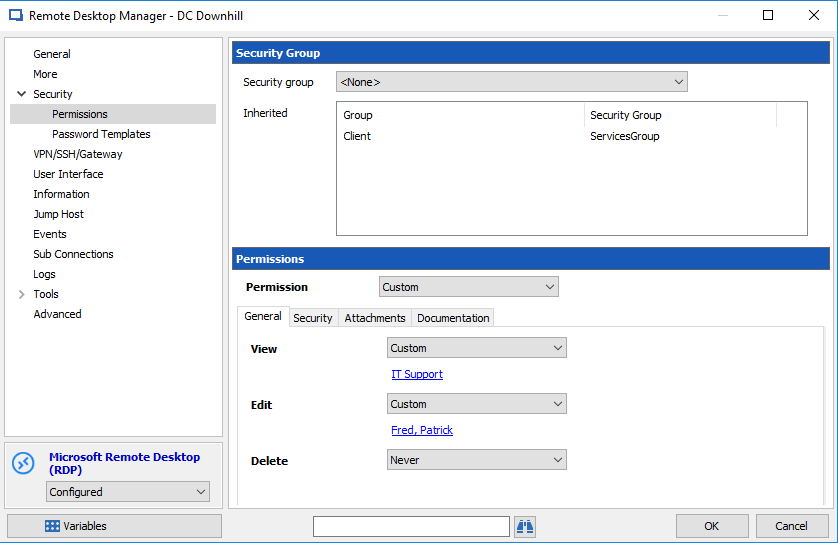
Role-Based Access Control System
- A role-based access control enables the creation of a granular protection system, giving the flexibility to manage more permissions.
- Only authorized users can get access to view, edit or manage permitted privileged accounts. Restrictions are enforced based on predefined user roles.
- Since all permissions are granular when using a role-based access control, multiple permissions can be set on multiple entries all at once.
- Security is inherited, which prevents users from creating entries without providing them with a sufficient security level.
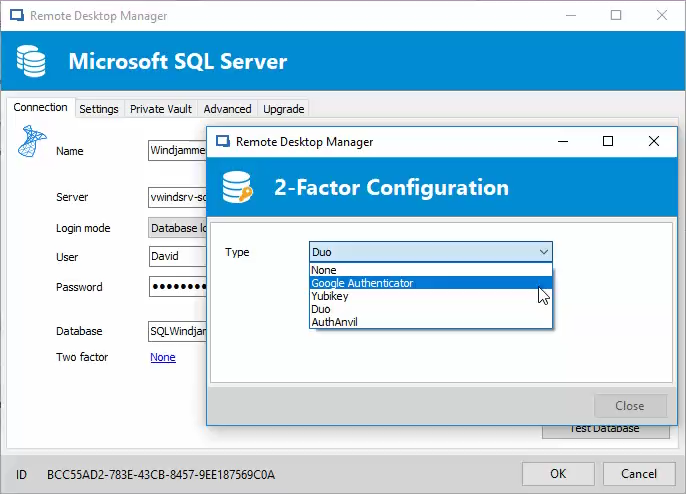
Two-Factor Authentication
- Two-factor authentication provides unambiguous identification of users through the combination of two different components. These components may be something the user knows or something the user possesses.
- Add an additional protection layer to your data source to ensure that only the right person has access.
- Remote Desktop Manager provides multiple two-factor authentication options, including: Devolutions Workspace, Duo, Google Authenticator, Yubikey and AuthAnvil.